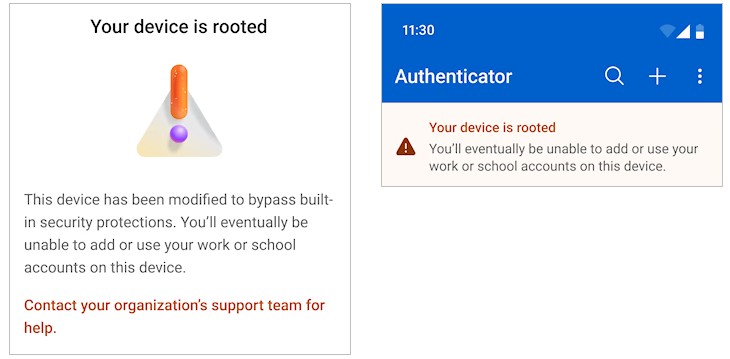
Microsoft has announced the General Availability of jailbreak and root detection in the Microsoft Authenticator app. The feature reached GA in February 2026 ( https://support.microsoft.com/en-gb/account-billing/jailbreak-root-detection-in-microsoft-authenticator-9f0431bd-675a-4f2d-b8fb-7acd18deaadc ) and applies to both iOS and Android devices.
The announcement is straightforward. What is worth clarifying is what this actually means in practice and where it matters more than it might first appear.
What Microsoft Announced
The Authenticator app now performs its own device integrity check. If a device is detected as jailbroken on iOS or rooted on Android, the app blocks access to any Entra ID credentials stored on it. This includes MFA approvals and passkeys enrolled on that device.
The detection happens at the app layer. It does not require Intune, Conditional Access, or any admin configuration in the Entra portal. The app makes the determination and enforces the block on its own.
What It Means in Practice
For tenants that already have Intune compliance policies flagging compromised devices as non-compliant, and Conditional Access requiring compliant devices, this announcement does not make a difference.
The more relevant scenario is a tenant without device compliance requirements attached to policies. In that case, a user on a jailbroken iPhone or a rooted Android device could previously open Authenticator, approve an MFA prompt, and access resources without any policy stopping them. That is what this change addresses.
For tenants with no Intune deployment and limited Conditional Access maturity, the impact is even more direct. Authenticator is now enforcing a device posture check that the tenant itself was not enforcing.
Important Details to Note
- No admin action is required. There is no toggle in the Entra admin centre and no Intune policy to deploy. The detection activates automatically as users update to the GA version of the app.
There is no documented override. Microsoft has not published a tenant-level setting to exclude users or devices from the detection. If a user is blocked, the resolution is to move to a non-compromised device. - The rollout is tied to app updates. Users on older versions of Authenticator will not be affected until the app updates. For most users, this will happen progressively through standard app store auto-updates.
- Passkeys are in scope. Users who have enrolled a passkey in Authenticator on a compromised device will also be blocked. Worth factoring in as passkey adoption increases.
- Jailbreak and root detection has known limitations. Detection evasion tools exist on both platforms, and certain Android configurations could produce false positives. Microsoft has not published details on the specific detection logic used.
What to Keep in Mind
Because this requires no admin action to activate, it will take effect without any deliberate rollout process. For tenants with Intune and Conditional Access configurations, the practical impact is limited.
For tenants with gaps in device posture enforcement, some users may encounter the block without prior warning.
Entra sign-in logs will show a failed or incomplete authentication, but the cause may not be immediately obvious from the log entry alone. It is worth making sure help-desk teams are aware of this before the first affected user calls in.
I hope this helps clarify what the announcement actually means.